Observability & Insights
Identity visibility meets control
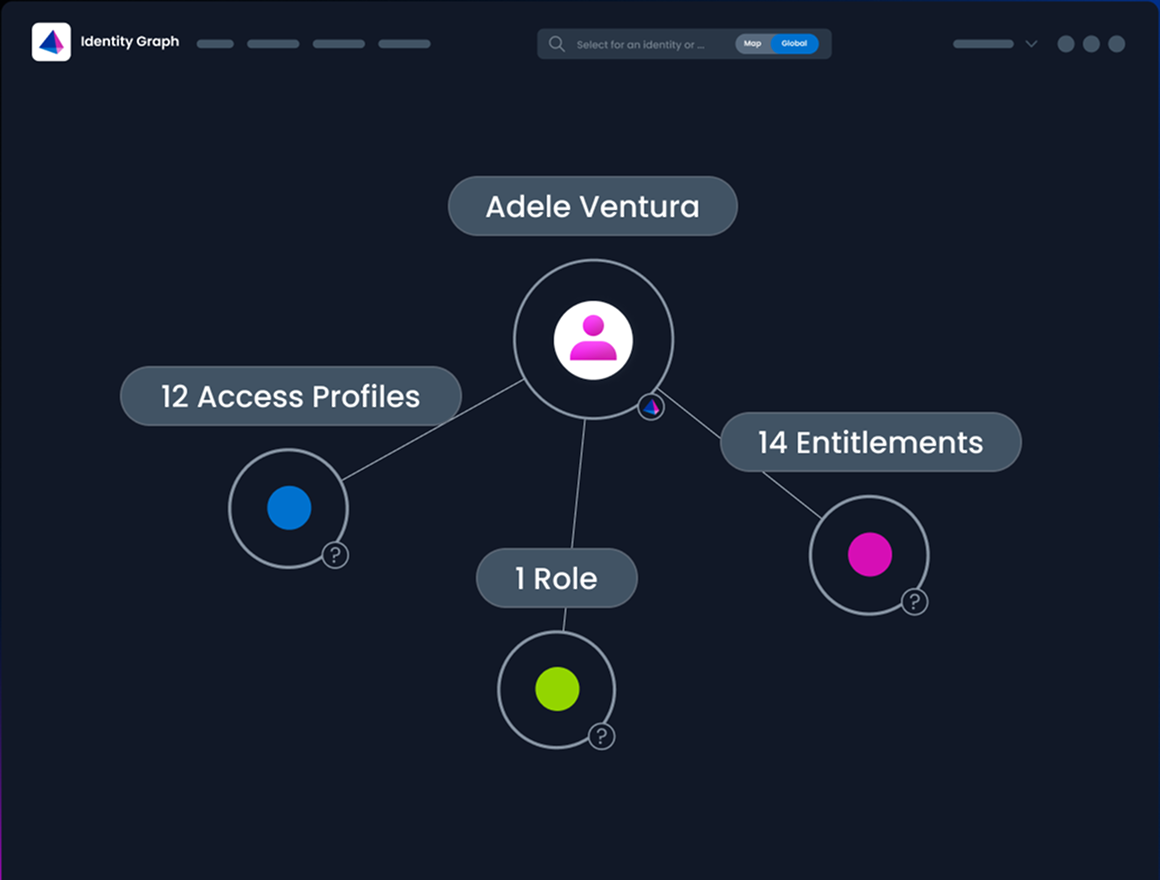
See every access path from every identity to your most sensitive data, then act on risk instantly from a single, unified view.

Challenge & solution
Turn complexity into insights and action
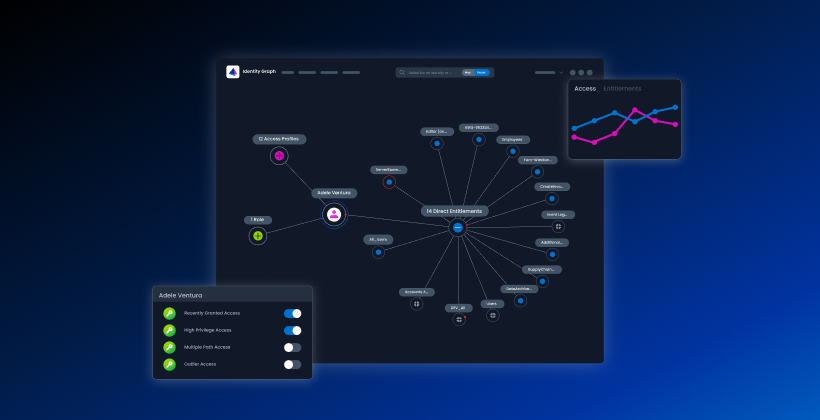
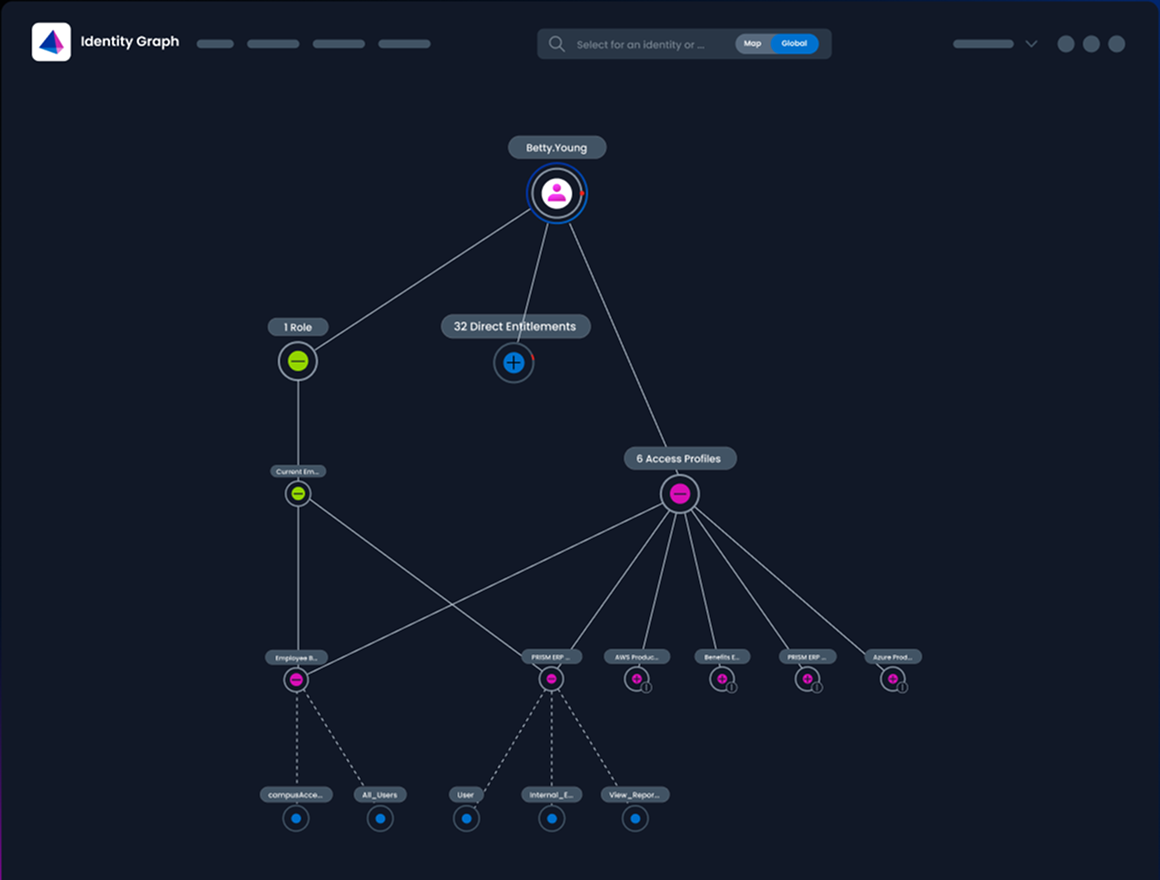
Every identity is a complex web of relationships—to roles, applications, entitlements, and data. When those connections become tangled and opaque, identity hygiene breaks down, allowing hidden attack paths to form and risk to grow. Visibility alone isn't enough; you need actionable intelligence.
SailPoint Observability & Insights, natively integrated in SailPoint Identity Security Cloud, untangles this complexity. It provides the visual clarity to understand your true security posture and the decisive control to act on risk instantly, all from a single, unified view.
The challenge
Fragmented systems hide the true path from identity to sensitive data
Complex access paths form hidden risks that traditional reviews miss
A flood of alerts without identity context buries real threats
Manual investigations for incidents and audits drain expert time
The solution
Visualize the complete path from any identity—human, machine, and agent—to sensitive data
Reveal and prioritize hidden risks with powerful contextual intelligence
Surface high-quality signals, like dormant-to-active behavior, to focus on what matters
Act instantly on risk with policy-driven controls directly within the identity graph

Use cases
Solving core challenges for every team
Deep visibility and contextual intelligence are the foundation for decisive action. Observability & Insights provides a unified visual map, empowering identity teams to improve identity hygiene and streamline governance, while arming security teams with the identity context to proactively hunt for risk and accelerate response.
Strengthen security posture
For security leaders, identity is the primary attack surface. Observability & Insights gives you the visual command needed to master this challenge.
Map your entire identity posture, tracing the true path from every identity—human and non-human— to sensitive data. The result: the confidence to answer the board's toughest questions, the evidence to validate that security policy is working, and the clarity to proactively reduce risk.
Streamline governance & audits
For identity teams, the daily reality is a tedious grind of managing complexity—a world of spreadsheets, disconnected logs, and endless access review tickets. Observability & Insights transforms this manual work into an intuitive, actionable workflow, directly in the identity graph.
Instantly untangle complex access paths and close tickets with one-click action. Cut audit preparation time by giving auditors a clear, visual history of access. This frees your team to focus on proactively improving identity hygiene instead of just trying to survive the spreadsheet grind.

Accelerate threat response
When a critical alert hits, an analyst's first question is, "What am I really looking at?" Alerts without identity context are just noise, burying real threats and delaying response. Observability & Insights cuts through that noise by enriching security alerts with the missing identity context.
This is the difference between guesswork and certainty. High-quality signals, like dormant-to-active behavior, instantly distinguish a real threat from a false positive. Your team can visualize the full blast radius in minutes, not hours, and deliver a precise, actionable remediation plan to the identity team.
See SailPoint in action
Explore on your own
Take a self-guided tour of SailPoint's identity security platform
Take product tourRelated resources
Observability & Insights resources
Start your identity security journey today
SailPoint Identity Security Cloud empowers organizations to intelligently manage and secure real-time access to critical data and applications.
Advanced capabilities
Take your identity security solution even further
SailPoint defines the future of adaptive identity for the AI-driven enterprise. Our comprehensive vision and AI-powered platform empower you to secure every identity—human and non-human—transforming risk into a powerful advantage and enabling confident AI innovation.
faq
Frequently asked questions
What is SailPoint Observability & Insights?
SailPoint Observability & Insights is an advanced capability within SailPoint Identity Security Cloud that provides an interactive graph of your identity & access environment. It maps relationships between identities, roles, entitlements, and access paths so you can instantly see who has access to what, how they got it, and whether it’s appropriate. By visualizing complex access patterns and surfacing risks such as redundant entitlements or rare access, it transforms identity data into actionable intelligence for better governance, stronger security, and faster decision-making.
How does it integrate with SailPoint Identity Security Cloud?
Observability & Insights is natively embedded within the SailPoint Identity Security Cloud. That means it leverages the same identity data and governance policies already in place, eliminating the need for additional connectors or external integrations. All context, metadata, and filtering tools are available directly within your SailPoint environment, providing a seamless extension of your existing identity security program.
Who benefits most — IAM, Security Ops, or CISOs?
All three audiences benefit, each in a distinct way:
- Security leaders gain visual command over the identity attack surface, using risk heatmaps and intelligence to prioritize investment and measurably improve their zero trust maturity.
- Identity teams eliminate tedious manual work, replacing spreadsheets with an intuitive graph to enforce least privilege and streamline governance.
- Security operations teams accelerate threat investigation by enriching alerts with identity context, enabling them to visualize the blast radius and deliver a precise, actionable plan to the identity team.
How does it help with compliance audits?
Audits often stall when teams must manually trace access across siloed records and applications. With Observability & Insights, every identity, entitlement, and access path is mapped in a single view, including nested and inherited permissions. This reduces manual effort, shortens audit cycles, and helps ensure your organization can demonstrate compliance with confidence and accuracy.
Can I take action directly from the graph?
Yes. This is a core part of moving from visibility to control. When risks are identified—such as an over-privileged or dormant account—you can take direct action to revoke the risky entitlement or de-provision the account entirely, directly from within the identity graph view
Contact us
Put identity security at the core of securing your business